Bloomberg is resurrecting the Super Micro spy chip story it first ran in 2018. The original story was met with blanket and unambiguous denials from everyone from Apple to the NSA, and the media company was roundly condemned for failing to either provide supporting evidence or retract the claim. Today, it is doubling down.
Today’s update claims that spy chips were found in Super Micro servers at the US Department of Defense …
Background
Here’s how we reported the original story in October 2018.
Bloomberg has today published a report claiming that companies including Amazon and Apple found Chinese surveillance chips in their server hardware contracted from Super Micro. Bloomberg claims Apple found these chips on its server motherboards in 2015. Apple is strongly refuting this report, sending out press statements to several publications, not just Bloomberg.
In a statement to CNBC, Apple said, “We are deeply disappointed that in their dealings with us, Bloomberg’s reporters have not been open to the possibility that they or their sources might be wrong or misinformed.”
Denials of the story were rapid and overwhelming. Apple said it had fully investigated the claims, and later provided off-the-record details of that investigation. I explained at the time the five reasons I believed Apple, with four more reasons emerging to make it abundantly clear that the Cupertino company was telling the truth.
It wasn’t just Apple denying the claim. The Department of Homeland Security did the same. One of Bloomberg’s sources told them the story made no sense. The NSA added its denial. A deep-dive analysis found the claims to be impossible. A Super Micro audit found no spy chips.
Super Micro spy chip story, take two
Bloomberg has today run a new report that initially reads as if it is a completely new story.
In 2010, the U.S. Department of Defense found thousands of its computer servers sending military network data to China—the result of code hidden in chips that handled the machines’ startup process.
In 2014, Intel Corp. discovered that an elite Chinese hacking group breached its network through a single server that downloaded malware from a supplier’s update site.
And in 2015, the Federal Bureau of Investigation warned multiple companies that Chinese operatives had concealed an extra chip loaded with backdoor code in one manufacturer’s servers.
Each of these distinct attacks had two things in common: China and Super Micro Computer Inc., a computer hardware maker in San Jose, California.
Super Micro has again denied the report.
In response to detailed questions, Supermicro said it has “never been contacted by the U.S. government, or by any of our customers, about these alleged investigations.” The company said Bloomberg had assembled “a mishmash of disparate and inaccurate allegations” that “draws farfetched conclusions.” Federal agencies, including those described in this article as conducting investigations, still buy Supermicro products, the company said.
You have to get some way into the piece before it references the original reporting.
Bloomberg Businessweek first reported on China’s meddling with Supermicro products in October 2018, in an article that focused on accounts of added malicious chips found on server motherboards in 2015. That story said Apple and Amazon had discovered the chips on equipment they’d purchased. Supermicro, Apple and Amazon publicly called for a retraction. U.S. government officials also disputed the article.
With additional reporting, it’s now clear that the Businessweek report captured only part of a larger chain of events in which U.S. officials first suspected, then investigated, monitored and tried to manage China’s repeated manipulation of Supermicro’s products.
As previously, most sources are anonymous, but a few are named as having been told about the claims, though without any firsthand knowledge.
“In early 2018, two security companies that I advise were briefed by the FBI’s counterintelligence division investigating this discovery of added malicious chips on Supermicro’s motherboards,” said Mike Janke, a former Navy SEAL who co-founded DataTribe, a venture capital firm. “These two companies were subsequently involved in the government investigation, where they used advanced hardware forensics on the actual tampered Supermicro boards to validate the existence of the added malicious chips” […]
“This was espionage on the board itself,” said Mukul Kumar, who said he received one such warning during an unclassified briefing in 2015 when he was the chief security officer for Altera Corp., a chip designer in San Jose. “There was a chip on the board that was not supposed to be there that was calling home—not to Supermicro but to China” […[
Mike Quinn, a cybersecurity executive who served in senior roles at Cisco Systems Inc. and Microsoft Corp., said he was briefed about added chips on Supermicro motherboards by officials from the U.S. Air Force. Quinn was working for a company that was a potential bidder for Air Force contracts, and the officials wanted to ensure that any work would not include Supermicro equipment, he said.
Bloomberg acknowledges the US government denials of its original coverage, and says that the NSA remains befuddled by the claims.
After Bloomberg reported on the added-chip threat in October 2018, officials for the U.S. Department of Homeland Security, the FBI, the Office of the Director of National Intelligence and the NSA made public statements either discounting the report’s validity or saying they had no knowledge of the attack as described. The NSA said at the time it was “befuddled” by Bloomberg’s report and was unable to corroborate it; the agency said last month that it stands by those comments.
You might want to ensure a decent supply of popcorn for the next few days.
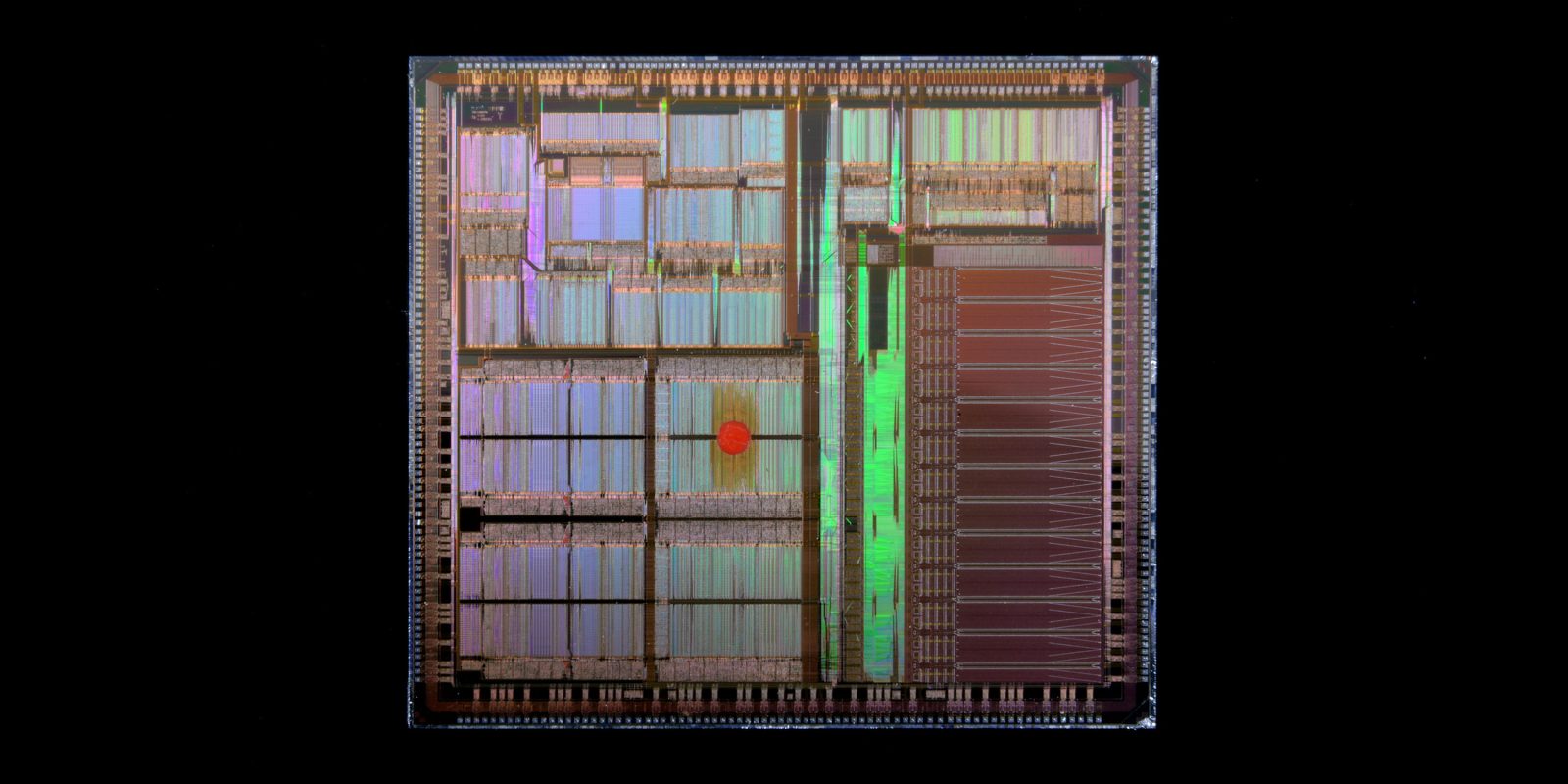
Photo by Laura Ockel on Unsplash
FTC: We use income earning auto affiliate links. More.


Comments